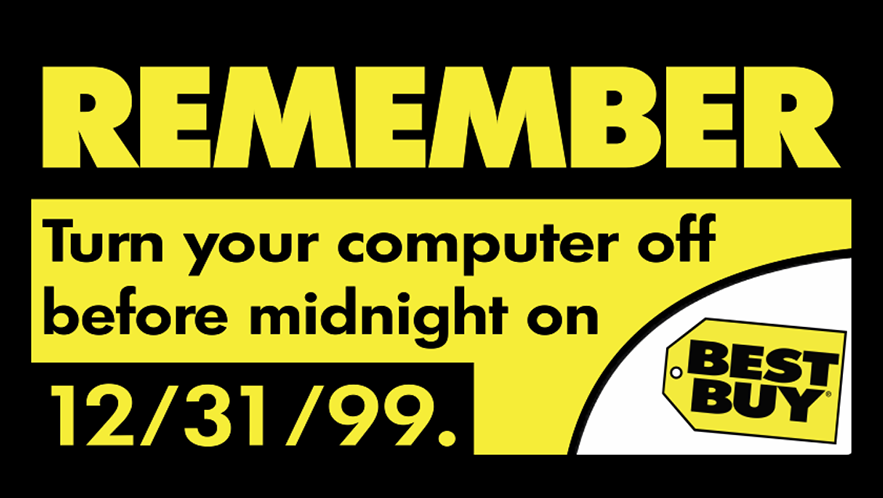
On the eve of the new millennium, the world collectively held its breath. The Y2K bug, also known as the Millennium Bug, loomed ominously, threatening to plunge computer systems into chaos and disrupt essential services worldwide.
Understanding the Y2K Bug:
The Y2K bug stemmed from a design flaw prevalent in early computer systems and software applications. Programmers, in an effort to conserve memory space, abbreviated the four-digit year to a two-digit format (e.g., 1998 as '98'). This practice worked well until the turn of the century, when the abbreviated year '00' was interpreted as 1900 instead of 2000. The glitch had the potential to wreak havoc on computer systems that relied on accurate date calculations, raising concerns about global infrastructure, financial markets, utilities, and essential services.
Preventive Measures and Remediation Efforts:
Recognizing the enormity of the potential disaster, governments, organizations, and IT professionals worldwide embarked on a mission to identify and remediate Y2K vulnerabilities. The scale of the task was staggering, requiring the meticulous assessment of countless lines of code across diverse systems.
-
Assessment and Inventory: Extensive audits and assessments were conducted to identify systems that were susceptible to Y2K issues. Organizations compiled inventories of hardware, software, and embedded systems that needed attention.
-
Code Remediation: Skilled programmers worked tirelessly to modify software applications and embedded systems to handle four-digit years correctly. This process involved searching for date-related code, correcting formatting issues, and implementing appropriate data validation techniques.
-
Testing and Validation: Rigorous testing was vital to ensure that remediated systems operated correctly and responded accurately to date-related scenarios. Various testing methods, such as date simulation, boundary testing, and stress testing, were employed to identify and rectify any remaining vulnerabilities.
-
Collaboration and Information Sharing: Governments and international organizations facilitated knowledge sharing and collaboration to tackle the Y2K bug on a global scale. This cooperative effort allowed experts to exchange best practices, raise awareness, and coordinate remediation efforts.
-
Contingency Planning: Despite the extensive remediation efforts, contingency plans were devised to handle any unforeseen issues. Emergency response teams and backup systems were put in place to address potential disruptions and ensure a swift response to critical situations.
Boson's own Michael Aldridge reflects what it was like working in the tech industry at that time.
In 1999, I was working for a telemessaging company. I was responsible not only for the computer systems across four locations, but also for the telecommunications equipment. Many long hours were spent installing patches and running tests, mostly at night to ensure that business-critical operations were not interrupted. To test, I would usually back up the system, then set the clock to 23:59 on December 31, 1999, to see what happened to our systems and data.
Michael Aldridge
As the last few seconds of 1999 ticked down, the world held its collective breath. Ultimately, the panic was overblown, as very few problems were experienced. Some say that the smooth transition was due to overpreparation, while others believe that the problems would have been insignificant even without preparation. However, current and future techs will get to experience the same sort of uncertainty when the "Y2K38 bug" hits on January 19, 2038, which will be caused by older UNIX clocks overflowing beyond their 32-bit limit.
If you want to meet the challenge of the Y2K38 bug, getting certified is a great first step and Boson can help you get there. Take advantage of our Summer Sale and save 25% off all digital products through June 30, 2023.