By James Hanback
If you were ever into mid-1980s computer gaming, you might know about a little graphical computer adventure game called King’s Quest. At the time, the game was developed and distributed by a company known as Sierra On-Line. King’s Quest was a role-playing adventure game, which meant that your goal as player was to guide the main character, Sir Graham, through the three-dimensional computer-generated Kingdom of Daventry. You walked Sir Graham around Daventry (and beyond) by using the keyboard. You made him perform other actions by typing verb and noun combinations or phrases like “take mirror” to gather items you would later use to solve puzzles that eventually (hopefully) enabled you to solve the game’s ultimate objective. Sometimes the game’s interpreter couldn’t figure out what you were telling Sir Graham to do, and those were the times that you’d need to get creative.
.NET Quest, Part I: Installing Boson Software in a non-Windows Environment
Jan 21, 2014 9:34:00 AM / by Kelson Lawrence posted in Dual Boot, Wine, Virtualization
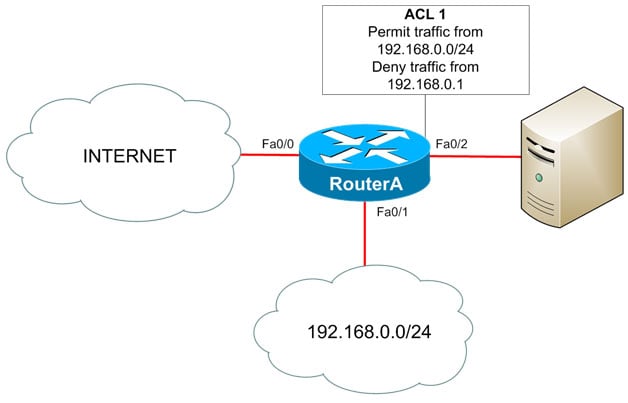
ACL Basics
Jan 14, 2014 3:45:00 PM / by Kelson Lawrence posted in Delana Hallstedt, permit, deny, syntax access-list, ACL basics, dysfunctinoal access control lists, standard ACLs, implicit deny rule
By Delana Hallstedt
If I were to start a conversation with my husband about a “broken ACL,” he would immediately panic and begin searching the Web for evidence that his beloved Megatron was free from injury and that his anterior cruciate ligament (ACL) was in perfect working order. Especially this time of year! Although I’m rather fond of the guy myself, for fantasy football purposes, that’s not the sort of ACL I’d most likely be referring to.
MS Windows 7 Tips and Tricks | 2.8.3 EFS – Part 1
Jan 9, 2014 8:39:00 AM / by Kelson Lawrence posted in NTFS, Encrypting File System, EFS Part 1
2.8.3 EFS – Part 1
By Val Bakh
As the world of information technology (IT) becomes more and more sophisticated with each passing day, the security of the information that we store on computers has become a major headache. But, just as we occasionally have to go to work while suffering a migraine, we have to accept the pervasive need for IT security. There’s no way around it. It’s like locking the door to your house when you are leaving for work. There’s always the risk that you might misplace your house keys during the day or leave them behind in your office, but leaving the door unlocked is no longer as viable an option as it used to be a few decades ago. Similarly, we have to secure our data. The question is, how? Data security is an extremely complex but fascinating subject area. There are many technologies and methods, which are usually implemented in conjunction with one another to form a multilayered, impregnable (keep your fingers crossed) fortress.
13 in '13 | Recapping the Year at Boson
Jan 2, 2014 9:10:00 AM / by Kelson Lawrence posted in certification, practice exams, courseware
By Kailin Acheson
2013 has flown by, and 2014 (our 15th anniversary!) is close on its heels. As we start the new year, I thought I'd share my top 13 highlights from the Boson World in 2013.